As enterprises increasingly transition AI workloads from testing to production on Google Kubernetes Engine (GKE), they leverage its scalability for robust inference endpoints. However, this shift brings unique security challenges, particularly as these models process sensitive data, exposing them to AI-related attack vectors such as prompt injection and data leakage.
To safeguard AI services, it is crucial to implement measures that protect against adversarial inputs and manage model outputs effectively. Developers are encouraged to utilize Model Armor, a guardrail service that integrates seamlessly with GKE Service Extensions, to create a secure and high-performance inference environment.
Understanding the Safety Challenge
Large language models (LLMs) typically incorporate internal safety mechanisms that prevent them from providing guidance on malicious actions. However, relying solely on these built-in safeguards presents several risks:
- Opacity: The refusal logic is embedded in the model weights, making it difficult to control.
- Inflexibility: Customizing refusal criteria to meet specific regulatory or risk management needs is challenging.
- Monitoring difficulty: Internal refusals often return a standard HTTP 200 OK response, masking potential threats from security monitoring systems.
Model Armor: A Strategic Solution
Model Armor serves as an intelligent gatekeeper by inspecting incoming traffic and outgoing responses. Integrated at the GKE gateway, it enhances security without necessitating changes to application code. Key features include:
- Proactive input scrutiny: Detects and blocks prompt injections and malicious URLs before they consume processing resources.
- Content-aware output moderation: Filters responses for harmful content based on configurable thresholds.
- DLP integration: Utilizes Google Cloud’s Data Loss Prevention technology to scan outputs for sensitive information, preventing data leakage.
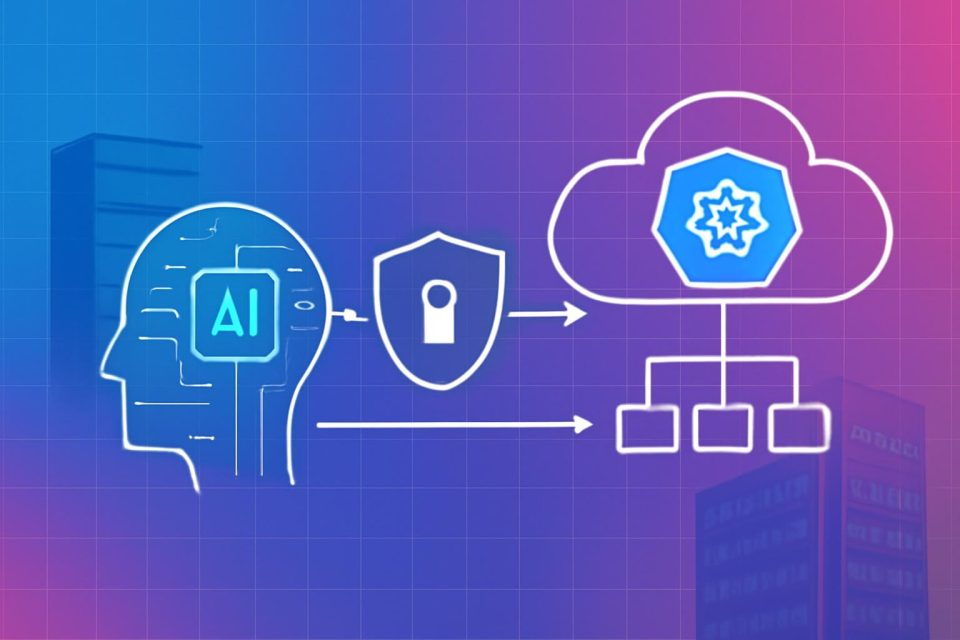
Architectural Overview
A balanced architecture combining GKE, Model Armor, and high-throughput storage can provide robust security:
- Request arrival: A user submits a prompt to the Global External Application Load Balancer.
- Interception: The request is intercepted by a GKE Gateway Service Extension.
- Evaluation: The request is evaluated by Model Armor against centralized security policies.
- If denied, the request is blocked at the load balancer; if approved, it proceeds to the model-serving pod.
- Inference: The model processes the request and generates a response using high-performance storage.
- Output scan: The response is checked again by Model Armor for compliance before delivery to the user.
Visibility and Control
Consider a scenario where a user inputs a harmful prompt. Without Model Armor, the model may politely refuse, but the system logs a successful transaction, leaving security teams unaware of the attack. In contrast, with Model Armor enabled, the harmful request is blocked, and the user receives a clear error message. This event is logged, providing transparency and allowing for audits of security incidents.
Moving Forward
To effectively secure AI workloads, a comprehensive defense strategy is essential. By integrating GKE orchestration with Model Armor and high-performance storage solutions, organizations can achieve centralized policy enforcement and enhanced visibility against adversarial threats, all without modifying existing model code.
For detailed implementation guidance, developers can refer to the complete tutorial available on the platform.